![Cisco Nexus 1000V Security Configuration Guide, Release 4.2(1) SV1(4) - Configuring TACACS+ [Cisco Nexus 1000V Switch for VMware vSphere] - Cisco Cisco Nexus 1000V Security Configuration Guide, Release 4.2(1) SV1(4) - Configuring TACACS+ [Cisco Nexus 1000V Switch for VMware vSphere] - Cisco](https://www.cisco.com/c/dam/en/us/td/docs/switches/datacenter/nexus1000/sw/4_2_1_s_v_1_4/security/configuration/guide/n1000v_security_6tacacs.fm/_jcr_content/renditions/n1000v_security_6tacacs-4.jpg)
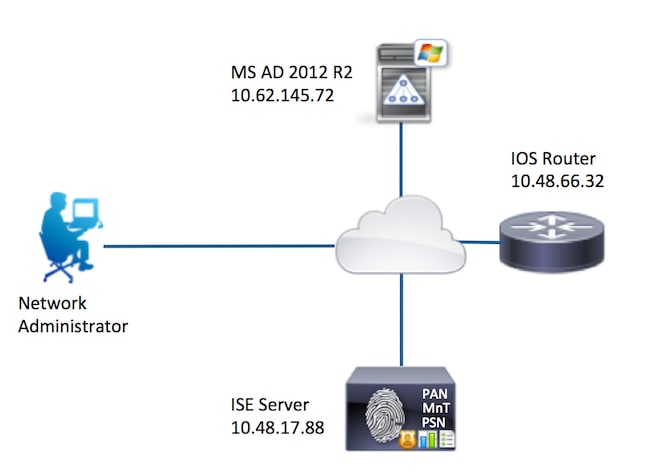
Cisco Nexus 1000V Security Configuration Guide, Release 4.2(1) SV1(4) - Configuring TACACS+ [Cisco Nexus 1000V Switch for VMware vSphere] - Cisco

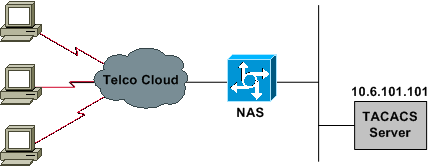
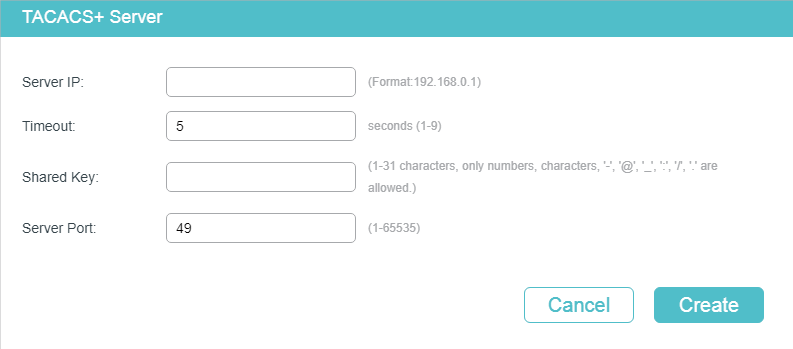
Warning: The cli will be deprecated soon 'tacacs-server host 10.0.0.200 key CCNP2 ' Please move to 'tacacs server ' CLI – The DEVNET GRIND!

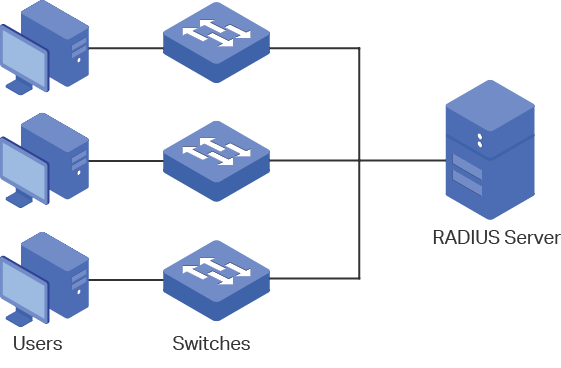
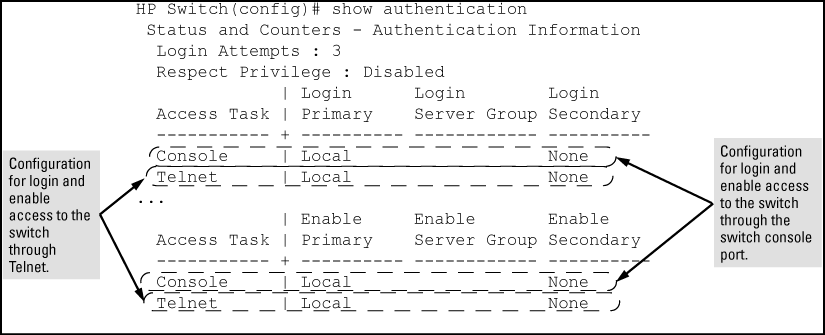
Solved: Cant enter enable mode after TACACS+ basic configuration - % Error in authentication - Cisco Community
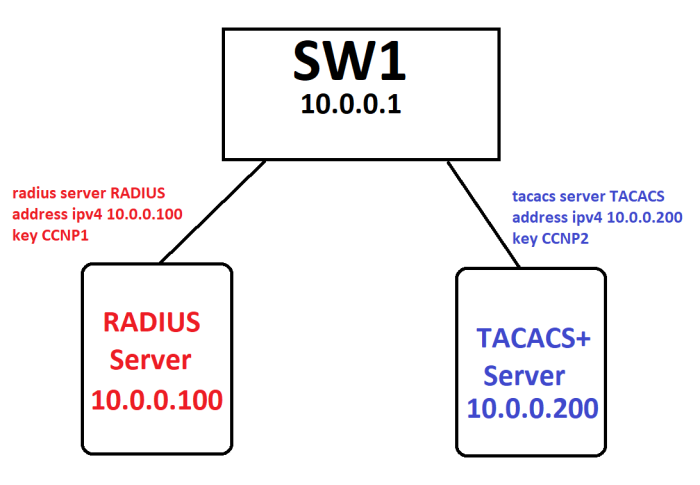
Warning: The cli will be deprecated soon 'tacacs-server host 10.0.0.200 key CCNP2 ' Please move to 'tacacs server ' CLI – The DEVNET GRIND!

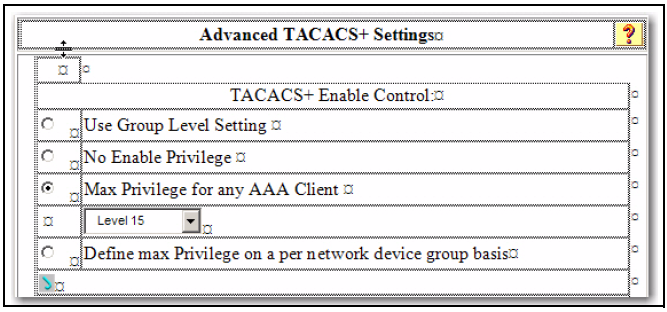
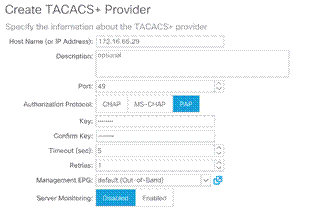
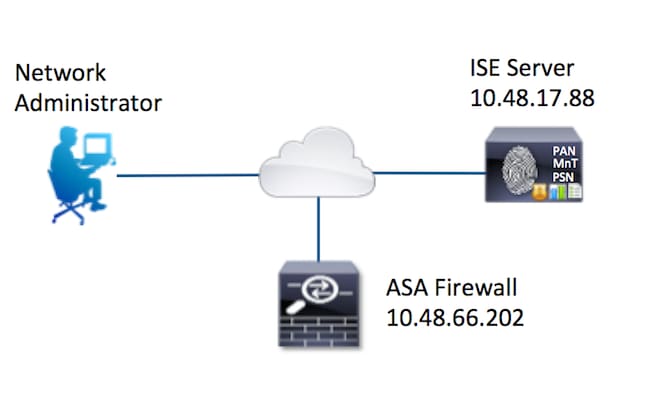
ACS 5.x: TACACS+ Authentication and Command Authorization based on AD group membership Configuration Example - Cisco